A UK initiative to measure the financial and economic impact of serious cyber attacks is to be replicated in the US, as organisations continue to face the risk of the highest level of attack.
After a year of operating in the UK, the Cyber Monitoring Centre (CMC), which measures the financial impact of cyber attacks on a 1 to 5 “hurricane scale”, plans to set up an operation to assess the financial impact of US cyber crime incidents.
The move comes as the UK faces risks from nation states in 2026, including China’s Volt Typhoon hacking group, which has been pre-positioning cyber attacks that could cause over £5bn of damage and impact tens of thousands of organisations.
“Volt Typhoon, if realised, is a Category 5 – lots of organisations and serious impact,” Ciaran Martin, founder of the National Cyber Security Centre and member of the CMC’s technical committee, told Computer Weekly.
Will Mayes, CEO of the centre, a non-profit company, told Computer Weekly that a US operation would begin in the background this year and is set to go live in 2027.
“We always felt that there would be interest, but now that we have proven the case in the UK, there is demand from organisations in the US to set up something there,” he said.
UK hit by two major cyber attacks in 2025
The Cyber Monitoring Centre, which began operations in February last year, has seen two major cyber events in 2025 that had significant financial implications for the UK.
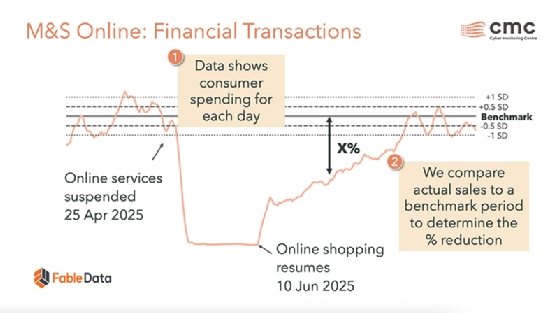
The CMC rated the cyber attack against Marks & Spencer and the Co-op, attributed to the Scattered Spider and DragonForce hacking groups, as a Category 2 cyber incident on its hurricane scale, with total costs between £270m and £440m.
The attack against Jaguar Land Rover (JLR) was a more severe Category 3 event, with an overall financial impact of £1.9bn. It materially affected the UK’s GPD.
The attack, linked to the Scattered Lapsus$ Hunters hacking collective, shut down JLR’s assembly lines and had a financial impact on more than 5,000 other organisations in JLR’s supply chain.
Attack data analysed by team of four to six people
The CMC deployed a team of four to six people working full time to analyse the impact of the hacking operation against Jaguar Land Rover for over a month.
The team, led by two actuaries, analysed publicly available data to estimate the financial impact of the attack. As a public limited company, JLR was unable to comment, but the team was able to speak to companies in the firm’s supply chain.
Their findings were reviewed and tested by CMC’s technical committee, a group of five experts – including Martin; professor of cyber security Sadie Creese; and former technology director of GCHQ Gaven Smith – in a half-day workshop to reach a final determination.
The CSC has identified the need to find better ways of predicting the cost for businesses to rebuild their IT systems following an attack, and is working with chief information security officers (CISOs) to find ways to make those calculations.
One of the lessons from both of the major attacks last year is the importance of investing in resilience, Smith told Computer Weekly. He gives the example of GCHQ, which, during the war, built 10 code-cracking Colossus computers, so that if one broke down, there were nine others standing by.
“That is an example from history I know, but there is a resilience strategy in there that executives ought to be paying attention to,” said Smith.
Companies lulled into false sense of security
NCSC’s Martin said companies have been lulled into a false sense of security since an expected wave of cyber attacks following Russia’s invasion of Ukraine failed to materialise.
“There was an assumption, putting it colloquially, that Western companies would get whacked by Russian cyber thugs in order to deter their governments from supporting Ukraine,” he told Computer Weekly. “That transparently did not happen.”
Today, minds are focused on the risks of cyber attacks from Iranian-affiliated hacking groups, as the war continues. Martin said Iran has form in this area, and is a sporadic but powerful user of disruptive cyber attacks when it feels threatened.
In 2012, for example, Iran targeted Saudi Aramco, then responsible for 10% of the world’s oil production, with its Shamoon malware, which wiped the data from over 30,000 computers.
In 2014, Iranian hacktivists targeted Las Vegas hotels, owned by Sheldon Adelson, an outspoken critic of Iran’s nuclear programme. And in 2024, Israel’s cyber chief called for a joint international front against Iranian hackers.
“That does not mean there is going to be an onslaught of cyber attacks that we feared from Russia that did not transpire, not least because so much of the regime’s cyber capabilities will have been destroyed,” he said.
Hacking groups affiliated to the Iranian regime will have been disrupted by internet blackouts across the country, and will be cautious venturing out onto the internet, said Adelson.
Hacking groups outside of the country could launch attacks like the one against the US medical technology firm Stryker this month, the only significant attack by Iran on a US organisation since the start of the war.
China could spark a Category 5 incident
A more serious risk could come from China. Chinese hacking group Volt Typhoon has targeted multiple CNI operators in Asia and across the US, pre-positioning for future attacks. Its presence in the UK is unknown.
Martin told Computer Weekly that a Volt Typhoon attack, if it happened, has the potential to be hundreds of times more damaging than the attack against Stryker. “It would be a Category 5,” he said.
“Even if Russia chooses not to do it for whatever reason, if the Iranians can’t do it for whatever reason, there are actors out there who can.”
